Freight Fraud Prevention: Why Cargo Theft Doubled (And How to Stop Ghost Carriers)
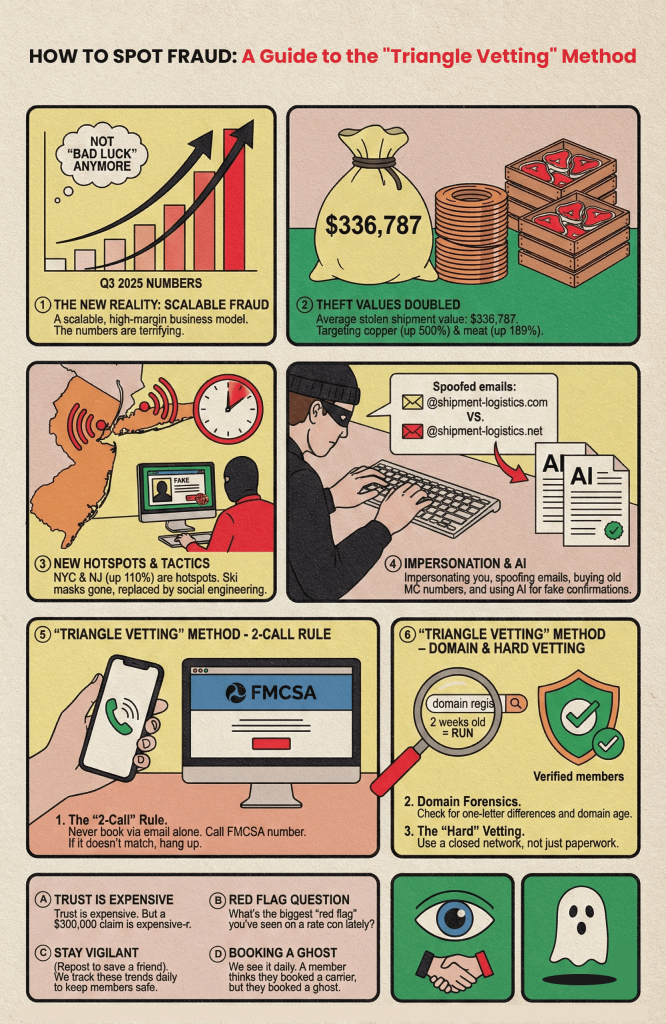
TL;DR: Freight fraud has evolved from opportunistic crime to a scalable, high-margin business model using AI and social engineering. Q3 2025 data shows average stolen shipment values hit $336,787 (doubled year-over-year), with strategic targeting of copper (+500%) and meat (+189%). New York/New Jersey has become the theft hotspot (+110%). Modern thieves don’t use ski masks—they spoof emails, buy legitimate MC numbers, and falsify rate confirmations with AI. The Triangle Vetting method (2-Call Rule, Domain Forensics, Hard Vetting) prevents the $300K+ losses that occur when you accidentally book a “ghost” carrier.
The New Reality: Freight Fraud as a Business Model
Freight fraud isn’t “bad luck” anymore. It is a scalable, high-margin business model.
We just saw the Q3 2025 numbers. They are terrifying.
The Data: Q3 2025 Cargo Theft Crisis
① Theft Values Doubled
The average stolen shipment is now worth US$336,787.
② Strategic Targeting (Not Random)
Thieves are targeting high-value, liquid commodities:
- Copper: ↑500% increase in targeted thefts
- Meat: ↑189% increase in targeted thefts
③ Geographic Concentration
NYC is the new hotspot. Theft in New Jersey surged up 110% last quarter, indicating organized groups have established operations in port corridors.
Key Insight: The “ski masks” are gone. They’ve been replaced by “social engineering.”
The Ghost Carrier Playbook: How Modern Freight Fraud Works
The scariest part of modern freight fraud? You book the carrier yourself.
Thieves are impersonating you. They are spoofing your emails. They are buying old MC numbers to look legitimate. They are using AI to falsify rate confirmations.
The Setup:
- Identity Harvesting: Purchase dormant Motor Carrier (MC) numbers with clean safety records from FMCSA
- Digital Camouflage: Create spoof websites with domain names one character off from legitimate carriers (shipment-logistics.com vs. shipment-logistics.net)
- AI Generation: Use AI tools to create professional rate confirmations, insurance certificates, and dispatch documents
- Social Engineering: Monitor load boards for high-value shipments, then undercut market rates by 10-15% to guarantee booking
The Result:
A member thinks they booked a carrier. In reality, they booked a ghost. The cargo disappears. The MC number traces to a defunct entity. The domain was registered two weeks ago. The phone number is a burner.
The Triangle Vetting Method: How to Stop a Ghost
We see it every day in the alliance. Here’s how we tell our members to use the “Triangle Vetting” method:
① The “2-Call” Rule
Never book via email alone.
Call the number on the official FMCSA SAFER file. Verify:
- Does the person who answers match the company name on the authority?
- Does the dispatcher know the driver’s name assigned to your load?
- Do they have physical terminal facilities at their listed address?
If the voice on the phone doesn’t match the FMCSA file—hang up.
② Domain Forensics
Email spoofing is the primary attack vector. Check:
- TLD Variations: Did the email come from @shipment-logistics.com or @shipment-logistics.net? That one-letter difference costs US$300K.
- Registration Date: Check the domain registration date via WHOIS. If it’s 2 weeks old—run. Legitimate carriers have domains registered for years.
- Spelling Variations: Look for subtle substitutions (1ogistics instead of logistics, fr8 instead of freight).
Red Flag: Recently registered domains with slight spelling variations from known carriers indicate fraudulent intent.
③ The “Hard” Vetting
Don’t trust the paperwork they send you.
Use a closed network where members are physically verified—not just digitally. Documents can be forged. AI-generated insurance certificates look perfect. But physical verification of terminals, equipment, and operations cannot be faked.
Hard Vetting Checklist:
- Satellite verification of terminal address (Google Earth street view)
- Physical inspection photos of trucks with company branding
- In-person or video-verified site tours of dispatch facilities
- References from known, established logistics companies (not just the references they provide)
Key Takeaways: Protecting Your Cargo in 2026
- 🔹 The $336K Reality: Average theft values doubled to $336,787—freight fraud is now big business with professional targeting
- 🔹 Strategic Commodities: Copper (+500%) and meat (+189%) are primary targets due to liquidity and resale value
- 🔹 Geographic Alert: NJ/NYC corridor theft surged 110%—exercise extreme caution with new carriers in this region
- 🔹 AI-Generated Fraud: Modern thieves use AI to create perfect fake rate confirmations and insurance docs
- 🔹 Triangle Vetting: The 2-Call Rule + Domain Forensics + Hard Vetting creates a verification perimeter that catches ghost carriers
- 🔹 Trust Economics: Vetting costs time; a US$300,000 claim costs your business
Frequently Asked Questions
What is freight fraud in logistics?
Freight fraud is the intentional deception of shippers or brokers by criminals posing as legitimate motor carriers to steal cargo. Modern freight fraud uses social engineering, email spoofing, and purchased MC numbers rather than traditional hijacking, making it harder to detect until cargo disappears.
How much does cargo theft cost on average?
As of Q3 2025, the average stolen shipment in freight fraud schemes is valued at US$336,787—representing a 100% increase from previous periods. High-value commodities like copper (up 500% in targeting) and meat (up 189%) are specifically sought by organized theft rings.
What is the Triangle Vetting method?
The Triangle Vetting method is a three-point verification system to prevent freight fraud: (1) The 2-Call Rule—verify carrier identity by calling FMCSA-listed numbers independently, (2) Domain Forensics—check for recently registered domains or slight spelling variations in email addresses, and (3) Hard Vetting—use physically verified closed networks rather than open load boards.
How do I spot a fake freight carrier (ghost carrier)?
Ghost carriers display these red flags: Email domains registered within 30 days, slight misspellings of legitimate carrier names (1ogistics vs logistics), rates 10-15% below market, refusal to provide video verification of facilities, and phone numbers that don’t match FMCSA SAFER system records.
Why is New Jersey a cargo theft hotspot?
New Jersey theft surged 110% in Q3 2025 because organized crime rings have established operations in the Port Newark/Elizabeth corridor, targeting high-value imports and exports with quick access to interstate highways for rapid dispersion of stolen goods.
What is the 2-Call Rule in freight broker security?
The 2-Call Rule requires brokers to call the phone number listed on the official FMCSA SAFER file (not the number provided by the carrier) to verify that the person answering represents the actual authorized carrier and knows the specific load details assigned to your shipment.
Implementation Checklist: Immediate Fraud Prevention Protocol
- [ ] FMCSA Verification: Cross-reference every new carrier’s MC number with the official SAFER system—check authority status, insurance expiration, and physical address
- [ ] Domain Audit: Run all carrier email domains through WHOIS lookup. Reject any domain registered less than 90 days ago
- [ ] The 2-Call Test: Call the FMCSA-listed phone number (not the dispatch number provided) to verify operational legitimacy
- [ ] Rate Reality Check: Flag any carrier quoting 10-15% below market rate without established relationship—this is the primary ghost carrier hook
- [ ] Documentation Forensics: Verify insurance certificates directly with the issuing agency (don’t trust emailed PDFs), check for AI-generated artifacts
- [ ] Geographic Caution: Implement enhanced scrutiny for NJ/NYC corridor pickups given the 110% theft surge
- [ ] Closed Network Migration: Shift from open load boards to vetted, physically verified carrier networks for high-value shipments (>$100K)
The Bottom Line
Trust is expensive. But a US$300,000 claim is expensive-r.
The thieves have upgraded their tools. They’ve replaced ski masks with social engineering and AI-generated documents. Your defense must upgrade too.
Stop booking based on the lowest rate. Start booking based on verified identity. The 10 minutes you spend on Triangle Vetting saves you from the 10 months you’ll spend dealing with a cargo theft claim.
What’s the biggest “red flag” you’ve seen on a rate con lately? Drop it below—let’s build a community defense database against these ghosts.